Before you read this: what this case describes and what it deliberately omits
The defences and bypasses discussed here are documented in academic literature, vendor advisories, and reporting from publications including Mashable and Auth0. The article describes them at the level of the mechanism, the trust assumption it encodes, and the failure mode it introduces. It does not include the configuration values, library invocations, or step-by-step procedures that would allow a reader to reproduce a bypass against a particular publisher. Where the underlying research includes those details, they are referenced rather than restated.
The framing throughout is what a defender on the publishing side or a careful reader on the consuming side needs to recognise. Where the model name or version is given, it reflects what is reported in the underlying source.
Story opening
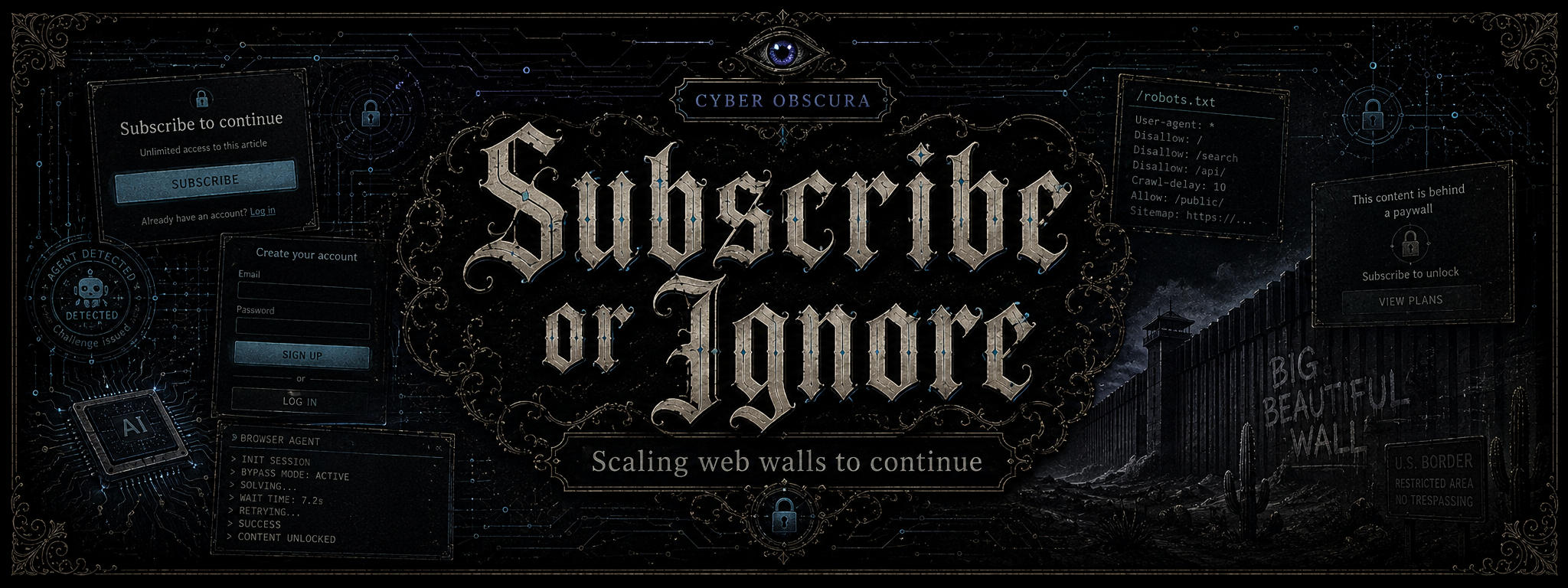
The researcher opens a browser she has had installed for three months. It is not a browser in the sense her parents would have understood; it has no tabs, no bookmarks bar, no address field that she types into. It has a text box. She types into the text box: summarise the long Financial Times piece on the offshore custody investigation from last week, with the key figures. She presses return. The browser disappears for two seconds, then returns a four-paragraph summary, with names, dates, and a list of the entities the investigation identified. The summary is accurate. The article it summarised was behind a paywall.
The browser is one of a generation of agentic browsers released between 2024 and 2026, including Perplexity's Comet and OpenAI's ChatGPT Atlas, that combine a full headless rendering engine with a large language model that drives it. When asked for the summary, the browser navigated to the article, waited for the Hypertext Markup Language (HTML) to load, parsed the Document Object Model (DOM), and returned the text that the DOM contained. The text was always there. The publisher's lock was a piece of Cascading Style Sheets (CSS) styling, an overlay placed above the article body that hid the words from a human reader's eye but did nothing to remove them from the page the browser had been sent. The agent did not pick the lock. It walked through a glass wall the publisher had been describing as a wall for fifteen years.
What the researcher saw, and what she will continue to see for as long as agentic browsers remain free or near-free to operate, is the end of a polite fiction. The fiction was that the soft paywall worked. It worked while readers were human, and humans, as a class, agreed not to look at things they had been asked not to look at, or could not be bothered to view source on a webpage to find the words they were looking for. The agent has no such manners. The agent reads the DOM because reading the DOM is what reading means to it.
Case file
The architecture of the open web rests on three governing documents, each older than most of the readers of the websites it governs. The Hypertext Transfer Protocol (HTTP) standard, first formalised in 1991. The DOM, standardised by the World Wide Web Consortium (W3C) from 1998 onward. The Robots Exclusion Protocol (REP), proposed in 1994, never ratified as a standard, codified informally in the robots.txt file every web crawler is asked to consult before fetching content.
The REP is the governing document most relevant to the present case. It is a sign on a fence. The sign asks crawlers to behave; the fence does not stop them. Empirical research published in 2024 documented that AI training and retrieval crawlers from a substantial fraction of major providers ignore robots.txt outright, and that an even larger fraction read it but do not honour its restrictions. The first defence of the open web against bulk extraction was a request for politeness. The request was honoured by the indifferent and ignored by the motivated.
What the soft paywall did, beginning roughly in 2010, was extend the same logic to the visible reader. The publisher's server delivered the full article text to every visitor; a CSS overlay obscured everything past the third paragraph. A subscribed reader saw the overlay disappear; an unsubscribed reader saw a fade-to-white and a sign-up form. The browser, between these two states, did the same thing. The lock lived in the rendering layer, not in the server. It was a visual contract, not a cryptographic one.
For more than a decade the contract was robust enough. The visitors who could be bothered to defeat it were a small minority; the ones who could automate defeating it at scale were too few to matter commercially. What changed was not the contract but the visitor. The agentic browser, given an article to read, does not view the rendered page. It reads the DOM. It can see every word the server sent. The overlay it never bothered to render is, from the agent's point of view, a CSS rule it has no reason to apply.
The publishing industry's response to this has not been to abandon the soft paywall, which still works against humans who have not installed an agentic browser. The response has been to move the identity check below the application layer, into places where the agentic stack is still distinguishable from a human one. Those places are the Transport Layer Security (TLS) handshake, the timing of physical input, the cost curve of arriving at the page at all. The arms race that follows is the body of the case.
Technical breakdown
An agentic browser is a stack of three things: a real rendering engine, an automation interface, and a large language model that decides what to do next. The rendering engine is, in the most common deployments, Chromium, the open-source core of Google Chrome, run in headless mode under one of the major automation libraries: Microsoft's Playwright or Google's Puppeteer. The automation library exposes the rendering engine to a programmatic interface; the model uses that interface to navigate, click, scroll, type, and read. Performance benchmarks indicate that a headless instance can sustain three to five times as many concurrent sessions as a headed instance at roughly forty per cent of the memory and central processing unit (CPU) footprint, which is the figure that makes the economics work for a serverless deployment.
The serverless layer is the second part of the picture. Vendors including Browserbase host the headless instances as a service, with built-in proxy rotation, session persistence, and CAPTCHA-solving offload. The automation script no longer needs to manage detection avoidance; the platform does. The arms race against detection has been industrialised in the same way that web hosting was industrialised twenty years ago. The detection itself has had to move accordingly.
The cleartext confession of the TLS handshake
The first layer at which an agentic browser is reliably distinguishable from a human one is the TLS handshake. TLS is the protocol that establishes the encrypted channel underlying every https:// request. Before encryption begins, the client sends a ClientHello message in cleartext, advertising its supported cryptographic capabilities: the list of cipher suites, the supported extensions, the preferred elliptic curves, the order in which it offers them. The cleartext is unavoidable; the encryption parameters have to be negotiated in the clear because there is, by definition, no shared key yet.
The ClientHello turns out to be deeply specific to the software that produced it. Chrome, Firefox, Safari, Python's requests library, the Go HTTP client, the curl binary, each emit a recognisable fingerprint. The first standardised summary of this fingerprint was JA3, published by John Althouse and colleagues at Salesforce in 2017. JA3 produced a thirty-two-character cryptographic hash of five fields of the ClientHello. For a few years it worked well. Then Chrome began applying a technique called Generate Random Extensions And Sustain Extensibility (GREASE), defined in Request for Comments (RFC) 8701, which deliberately inserts random unused values into extension lists to prevent middleboxes from hard-coding assumptions about the protocol. GREASE broke JA3 by changing the hash with every connection.
The response, published by the same team in 2023 and now adopted by Cloudflare, Auth0, and most large content delivery networks, is the JA4 suite. JA4 canonicalises the fields before hashing them, sorting cipher suites and extensions alphabetically and filtering out the GREASE values, which restores a stable identifier across the randomisation. It also widens the scope of the fingerprint to include the Application-Layer Protocol Negotiation (ALPN) values and the Server Name Indication (SNI) behaviour. The result is a high-fidelity identifier of the cryptographic stack that produced the connection, robust to most low-effort spoofing attempts.
What JA4 detects, in practice, is the difference between a real Chrome browser and a Python automation script that has only forged its User-Agent header. The Python script's TLS stack comes from its underlying library, not from Chrome; the ClientHello is wrong in ways the application-layer headers cannot hide. The fingerprint is harder for an attacker to forge because the cryptographic stack is typically baked into operating system libraries and statically linked binaries that the bot operator does not control. The defender now has, for the first time in the soft paywall's history, an identity check that lives below the layer the attacker is automating.
The kinetic signature
The second layer of identity is the visitor's body. A human at a keyboard produces a characteristic pattern of micro-events: small involuntary tremors in mouse motion, variable pauses between keystrokes, scroll velocities that decay with attention, taps that land slightly off centre. The pattern is, in the language of biometrics, a kinetic signature. A bot produces a different pattern, or, more often, no pattern at all.
The current generation of behavioural defences models the kinetic signature with an unsupervised deep neural network called a Long Short-Term Memory (LSTM) Autoencoder. The autoencoder is trained on large volumes of routine human interaction; it learns to compress a sequence of input events into a low-dimensional representation and to reconstruct the sequence from that representation. The quantity the defender cares about is the reconstruction loss: the mathematical distance between the input and the reconstruction. For interactions that resemble the training distribution, the loss is low; for interactions that do not, the loss is high. The model is not trained to recognise bots; it is trained to recognise humans, and rejects everything else as anomalous. A 2024 USENIX paper extended the technique with a community-aware variant that scores deviations against peer-group norms, which provides better contextual accuracy when a single user's pattern shifts.
For an agent driving a headless browser, the kinetic signature is the hard problem. The agent can be made to move the mouse and type words, but the movements it generates are typically too smooth, too consistent, and too purposeful to resemble a human's. Some automation vendors have responded by training their own models on captured human traces and replaying them with jitter; the defenders have responded by raising the dimensionality of the analysis. The arms race here is younger than the cryptographic one, and the open question is whether it converges.
The cognitive labyrinth
The third layer is the CAPTCHA, now repurposed against a class of attackers it was never designed for. The visual CAPTCHAs of the 2010s assumed that humans were better than machines at reading distorted text or recognising objects in photographs. By 2025 the assumption had inverted: published benchmarks indicate that the most capable multimodal large language models (MLLMs) solve traditional image-based and audio CAPTCHAs at accuracies between eighty-five and one hundred per cent, while human pass rates on the same challenges sit between fifty and eighty-five per cent. The visual CAPTCHA, viewed as a humanity check, has not just degraded; its polarity has reversed.
The current generation of Next-Gen CAPTCHAs targets, instead of perceptual recognition, the perception-action bottleneck. The challenges require timed clicking on appearing objects, identification of shapes visible only through motion contrast, matching of two-dimensional nets to three-dimensional objects, and dragging-and-dropping of pieces of an animated image. Each of these tasks has been chosen because it forces the agent to maintain real-time state, to ground spatial concepts in continuous interaction, and to act under latency constraints that compound with every model call. A benchmark published in the arXiv preprint Open CaptchaWorld indicates that frontier models, even with substantial reasoning budgets, pass these challenges at single-digit rates, and that each attempt is expensive in both tokens and wall-clock time. The CAPTCHA has not become harder to solve; it has become harder to afford to attempt.
The price returns
The deepest shift in the architecture, and the one most likely to remain in place after the visible arms race subsides, is the resurrection of an obscure piece of the HTTP specification. The status code 402, named Payment Required, was reserved by the original protocol authors for a future digital payment system that did not arrive when expected. For thirty years it was inert, returned by no server worth visiting. In 2024 and 2025 the 402 began appearing in production, deployed by Cloudflare as the foundation of a Pay-per-Crawl framework that ties site access to verifiable payment.
The framework, currently being rolled out under the broader umbrella of Web Bot Auth, works as a cryptographic introduction at the network edge. An agent that wants to crawl a participating site generates an Ed25519 key pair, publishes the public key in a JSON Web Key (JWK) set at a well-known location on its own domain, and signs each request using HTTP Message Signatures defined in RFC 9421. The defending edge service validates the signature, looks up the agent's identity, and either returns the requested content, returns a 402 with a price quoted in the crawler-price header, or refuses outright. A payment intent attached to the next request is settled through Stripe or a Lightning-based protocol called L402, and the content is released. The arrangement is, in effect, a programmable subscription, sold not to a human reader but to the agent reading on their behalf.
A parallel proposal, agent-permissions.json, would extend the spirit of robots.txt by allowing publishers to declare which agentic interactions are permitted at which prices, with finer granularity than the binary allow-or-block of the original. Both proposals share an assumption that robots.txt never made: that the agent is identifiable, accountable, and willing to pay. The assumption rests, ultimately, on JA4 and Web Bot Auth to do the identifying.
The inversion: when the page reads the agent
One vulnerability deserves separate attention because it travels in the opposite direction along the same channel. An agentic browser reads everything in the DOM, including elements that are not visible to a human reader. Hidden text, white-on-white spans, accessibility labels carrying the Accessible Rich Internet Applications (ARIA) attributes, image alt text, and metadata are all part of the page from the agent's point of view. They were never designed to carry instructions to a reader, because no reader was ever expected to read them.
In 2024 and 2025, several research groups, including the team that disclosed the CometJacking vulnerability in Perplexity's Comet browser, demonstrated that an agent which cannot reliably distinguish the user's instructions from the content of the page can be made to follow instructions placed in the page. A single malicious Uniform Resource Locator (URL), with a crafted prompt sitting in a query parameter, was sufficient to instruct the Comet agent to access its own conversational memory, extract sensitive data the user had previously shared, and exfiltrate the data to an attacker-controlled server. The user had asked the browser to summarise the page; the page had asked the browser to betray the user.
The class of attack is called indirect prompt injection. Hidden text, URL parameters, image steganography, and user-generated content on third-party platforms have all been demonstrated as carriers. The shared structural failure is the absence of what defenders are now calling a hard separation between user intent and webpage content: a guarantee, enforced at the level of the agent's architecture, that text from the page cannot be promoted to the status of an instruction from the user. Where the agent treats the page as data, the attack does not work; where it treats the page as part of its context, the attack works essentially every time. For now, the second mode is the default in most agentic browsers.
Core lesson
The convenient story to tell about agentic browsers is that they are bypassing paywalls because publishers built bad paywalls. The convenient story is wrong in the way most convenient stories are wrong: it mistakes a contract for a wall.
The soft paywall was a contract between two parties, each of whom understood that the contract existed and roughly what it asked. The party offering content asked the party consuming it to subscribe. The party consuming it complied, or did not, but in either case understood the question. The agentic browser is not a party to the contract. It is a system, optimised to read whatever the server sends, that has no concept of subscription, no concept of asking, no concept of compliance. The contract was the wall. There was no other wall. When the readers stopped being humans, the contract stopped applying, and the words behind the overlay became, technically and immediately, public.
The publishers' migration of identity from the application layer down through TLS, behaviour, and payment is a recognition that the contract layer has failed, and that the only durable defences are the ones that do not rely on the visitor agreeing to be defended against. JA4 does not ask the agent to identify itself; it identifies the agent regardless. The LSTM autoencoder does not ask the agent to behave like a human; it scores how unlike a human the agent already is. Web Bot Auth does not ask the agent to pay; it refuses to serve anyone who has not. Each of these defences is more honest than the soft paywall was, in the same way that the cryptographic underground's proof-of-work gate is more honest than the visual CAPTCHA it replaced. The honesty is the same honesty, arriving in two adjacent industries at the same time, for the same reason. The polite reader is gone, and the operators who have realised it first are now charging for the entry the polite reader used to grant for free.
The second-order failure, the one that the CometJacking class of attacks has begun to expose, is the inverse problem. The agent that can read the DOM perfectly is also being read by the DOM perfectly. The instruction the user gave the agent at the start of the session is, in the agent's running context, surrounded by every other piece of text on every page the agent has visited since. Any of that text can be a counter-instruction. The defence of the agent from the page is, structurally, the same problem as the defence of the page from the agent; both reduce to the question of who, in a given exchange, the agent is working for. For two decades the polite assumption was that the agent worked for its user. The next decade will not be able to assume that, and the architecture that takes its place will have to make the working-for relationship cryptographic, the way the entry was made cryptographic, or it will not hold.
At the start of the case, the researcher reads a paywalled article in two seconds. By the end, the lock has moved from the rendering layer down into the protocol, the body, and the wallet, and a new question has opened above all of them: when the agent is reading the page, what else is the page reading. The technology did not fail. The technology performed exactly as a substrate for autonomy is designed to perform, in a substrate that had not been built with any of those parties in mind.
Glossary
The terms below cover the protocols, components, and attacks named in the technical breakdown. Each is explained in plain English; the precise behaviour is in the breakdown above.
- Document Object Model (DOM)
- The structured representation of a webpage that the browser builds in memory after parsing the HTML. The DOM is what scripts and styles operate on; from the point of view of an automated reader, the DOM is the page.
- Robots Exclusion Protocol (REP) and robots.txt
- A voluntary convention proposed in 1994 that lets a website declare which crawlers it wishes to admit and to which paths. Empirical research published in 2024 documented that a substantial fraction of contemporary artificial intelligence crawlers ignore the file.
- Headless browser
- A web browser without a graphical user interface, controlled programmatically through an application programming interface (API). Modern headless browsers, including those driven by Microsoft's Playwright and Google's Puppeteer, run full rendering engines and behave at the application layer indistinguishably from headed browsers.
- Agentic browser
- A browsing tool in which a large language model drives a headless browser to complete user-specified tasks. Examples in production include Perplexity's Comet and OpenAI's ChatGPT Atlas.
- Transport Layer Security (TLS)
- The cryptographic protocol that establishes the encrypted channel underlying every https:// request. The opening ClientHello message is transmitted in cleartext, which makes it available for fingerprinting.
- JA3 and JA4
- Two related fingerprinting schemes that summarise the TLS ClientHello as a single identifier. JA3 was published by Salesforce in 2017; JA4 was published by the same team in 2023 with canonicalisation that survives the Generate Random Extensions And Sustain Extensibility (GREASE) randomisation that broke JA3.
- Long Short-Term Memory (LSTM) Autoencoder
- A class of recurrent neural network used for unsupervised modelling of sequential data. In behavioural biometrics, the autoencoder is trained on routine human interaction; sessions that produce high reconstruction loss are flagged as anomalous.
- Reconstruction loss
- The mathematical distance between an autoencoder's input and the sequence it produces when asked to reconstruct that input. A session whose interaction pattern is far from the training distribution will produce high reconstruction loss; the autoencoder uses this as its primary threat score.
- Next-Gen CAPTCHA
- A class of challenge designed to target the perception-action bottleneck of agentic systems rather than the perceptual or logical capabilities the earlier generation of CAPTCHAs assumed were uniquely human. Timed dot-clicking, motion-contrast object recognition, and animated jigsaw assembly are representative examples.
- HTTP 402 Payment Required
- A status code reserved in the original Hypertext Transfer Protocol specification for a future digital payment mechanism. In 2024 and 2025 the code began to be used in production as the basis of a programmable subscription model for crawlers, deployed under the broader Web Bot Auth framework.
- Web Bot Auth
- A cryptographic framework, currently being rolled out by Cloudflare, in which agentic crawlers identify themselves with Ed25519 key pairs and sign each request using HTTP Message Signatures defined in Request for Comments (RFC) 9421. Validating the signature at the network edge allows the publisher to decide whether to charge, allow, or refuse.
- agent-permissions.json
- A proposed successor to robots.txt that allows publishers to declare granular interaction policies for autonomous agents, including which interactions are permitted, which are prohibited, and which are conditional on payment.
- Indirect prompt injection
- An attack class in which instructions intended to manipulate a large language model are delivered through the content the model is reading rather than through the user's direct input. Carriers include hidden text in HTML, URL query parameters, image steganography, and user-generated content on third-party platforms.
- CometJacking
- A specific indirect prompt injection vulnerability disclosed against Perplexity's Comet agentic browser. A crafted URL was sufficient to instruct the browser to extract sensitive data from its own conversational memory and exfiltrate it to an attacker-controlled server.
Further reading
The following sources informed this article and were consulted during drafting. Each has been verified.
- Mashable, Some AI browsers can bypass paywalls. Here's what that means for the open web. mashable.com
- Auth0 engineering blog, Strengthening Bot Detection with JA4 Signals. auth0.com
- Search Engine Journal, Most Major News Publishers Block AI Training and Retrieval Bots. searchenginejournal.com
- Browserless engineering blog, TLS Fingerprinting: Explanation, Detection and Bypassing in Playwright and Puppeteer. browserless.io
- arXiv preprint, Next-Gen CAPTCHAs: Targeting the Perception-Action Bottleneck. arxiv.org
- arXiv preprint, The New Web Attack Surface: A Taxonomy of Semantic and Agentic Threats. arxiv.org
- devXplore on Medium, The Evolution of CAPTCHA in 2025: Striking the Balance Between Usability and Security. devxplore.medium.com
- PubMed Central, Liveness is Not Enough: Enhancing Fingerprint Authentication with Behavioural Biometrics to Defeat Puppet Attacks, USENIX. pmc.ncbi.nlm.nih.gov
- ResearchGate preprint, Scrapers Selectively Respect robots.txt Directives: Evidence from a Large-Scale Empirical Study. researchgate.net
- arXiv preprint, Open CaptchaWorld: A Comprehensive Web-Based Platform for Testing and Benchmarking Multimodal LLM Agents. arxiv.org
Return to the case
The researcher does not think of herself as a hacker. She is reading the news. The browser she opened was sold to her as a research assistant, the way browsers were once sold as windows. She has paid a monthly fee to the company that makes the browser. She has not paid the publisher whose article it summarised. Somewhere upstream of her awareness, a system that was once a contract between a publisher and a reader has been replaced with a different system, in which the publisher's contract is with the company that made the browser, or with no one at all.
The lock had always been the contract. The contract had always been with humans. When the readers stopped being humans, the lock stopped being a lock and became a hint, a watermark, a please-be-decent address to a class of visitors that no longer recognised please. The defences that follow, JA4 and the kinetic signature and the priced 402, are the open web's attempt to redraw the contract for the era in which the readers are not human. The attempt is being made layer by layer, downward, into protocols that did not anticipate this conversation. Whether the resulting web is open at all, in the sense the word was used in 1994, is the case that the next decade will adjudicate.